How to use our product
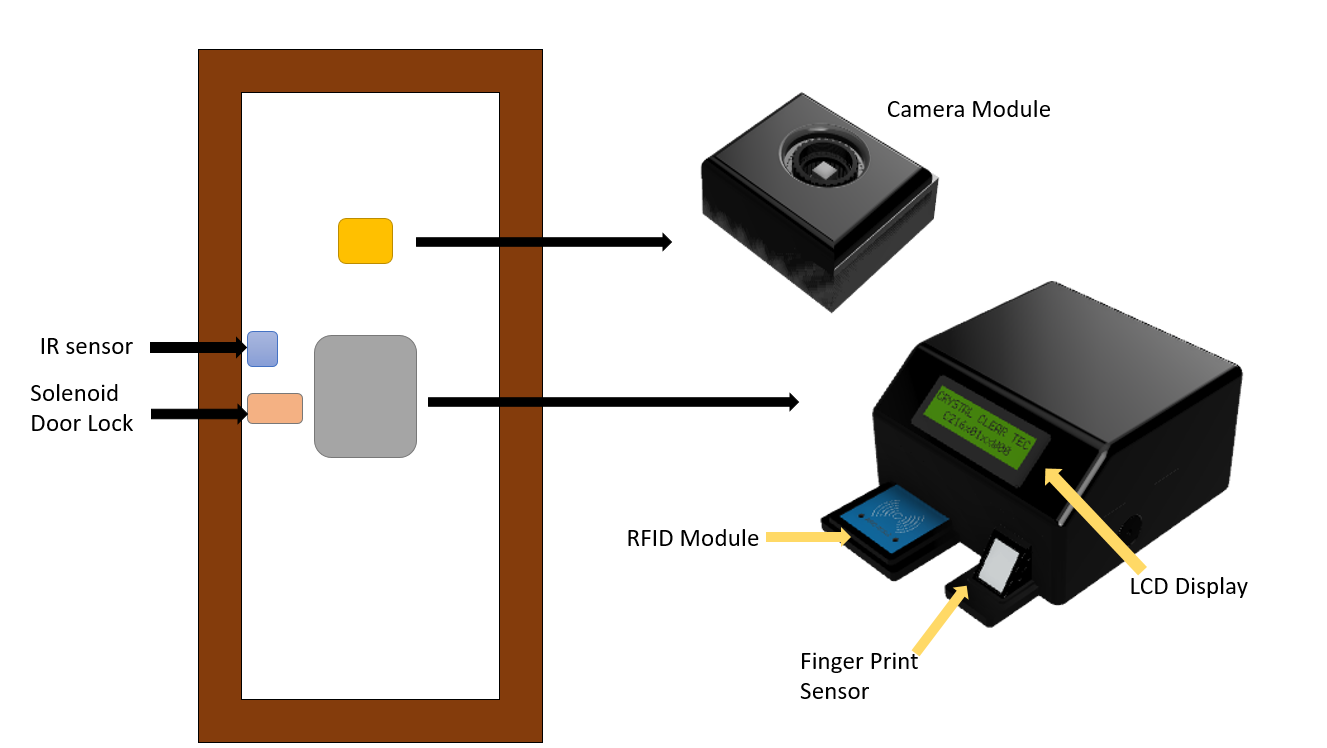
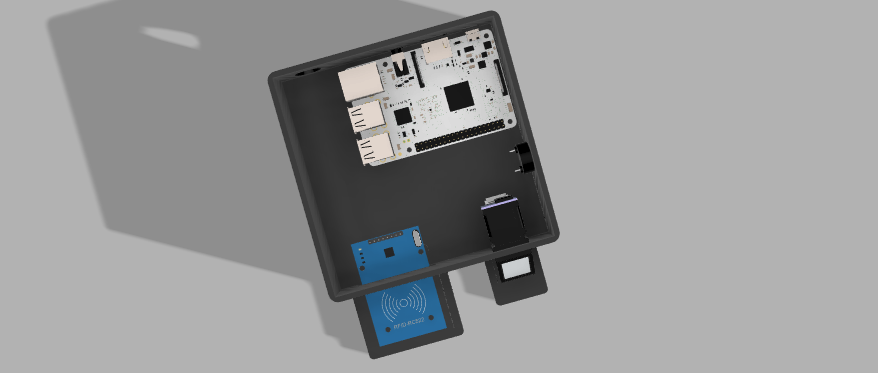
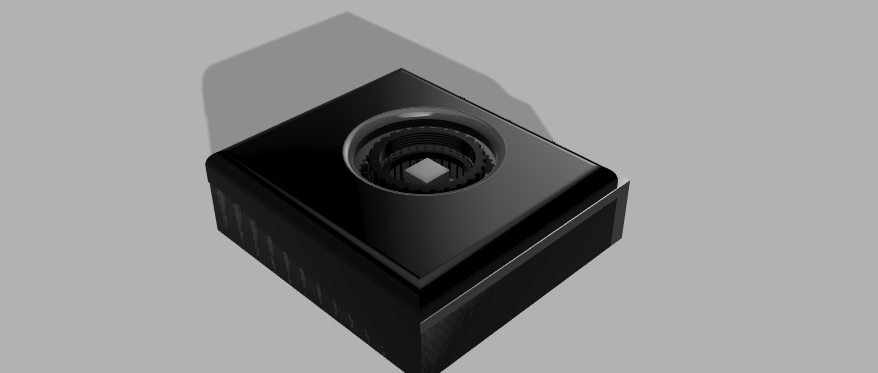
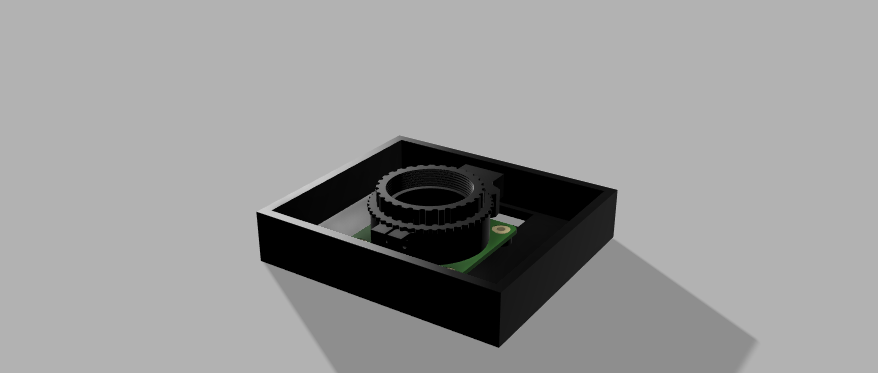
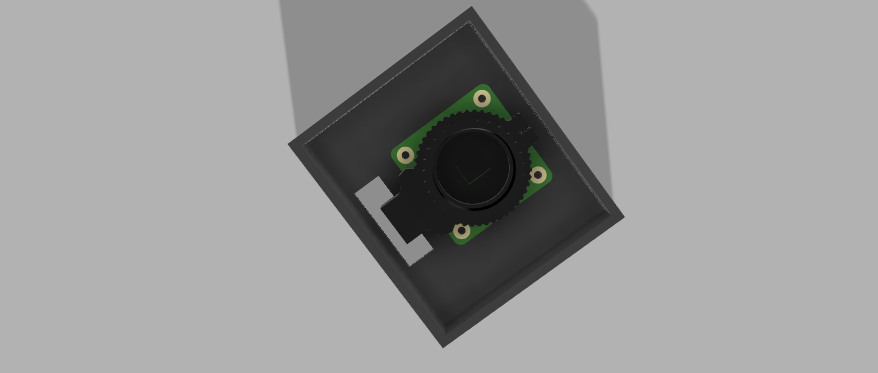
As we mentioned in the introduction there are several reasons to prove that tradition door lock systems at the entrance are inefficient. But in this product we have overcome all those problems and give a quick access to the door user while providnig important addtional services such as take access records and giving realtime update about the access using a lcd display
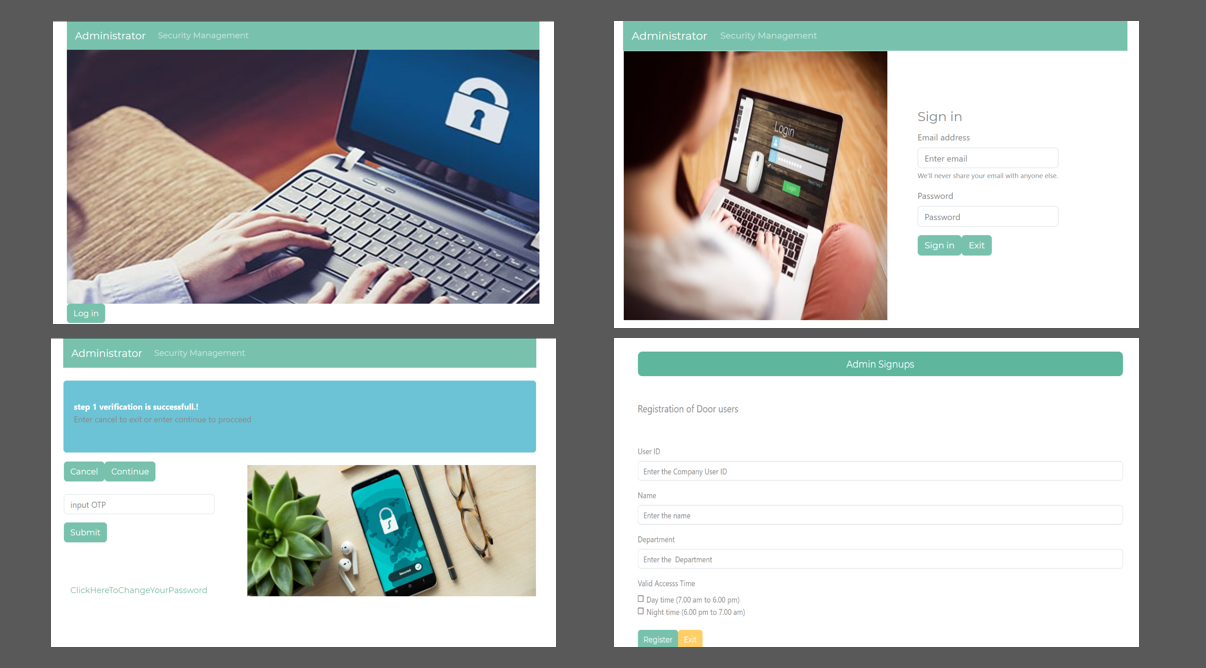
Register Users
In order to register an user, administrator should fill the form provided in the website with uniquely provided userid. Here, the corresponding userid is registered for one specific person.
Access Given
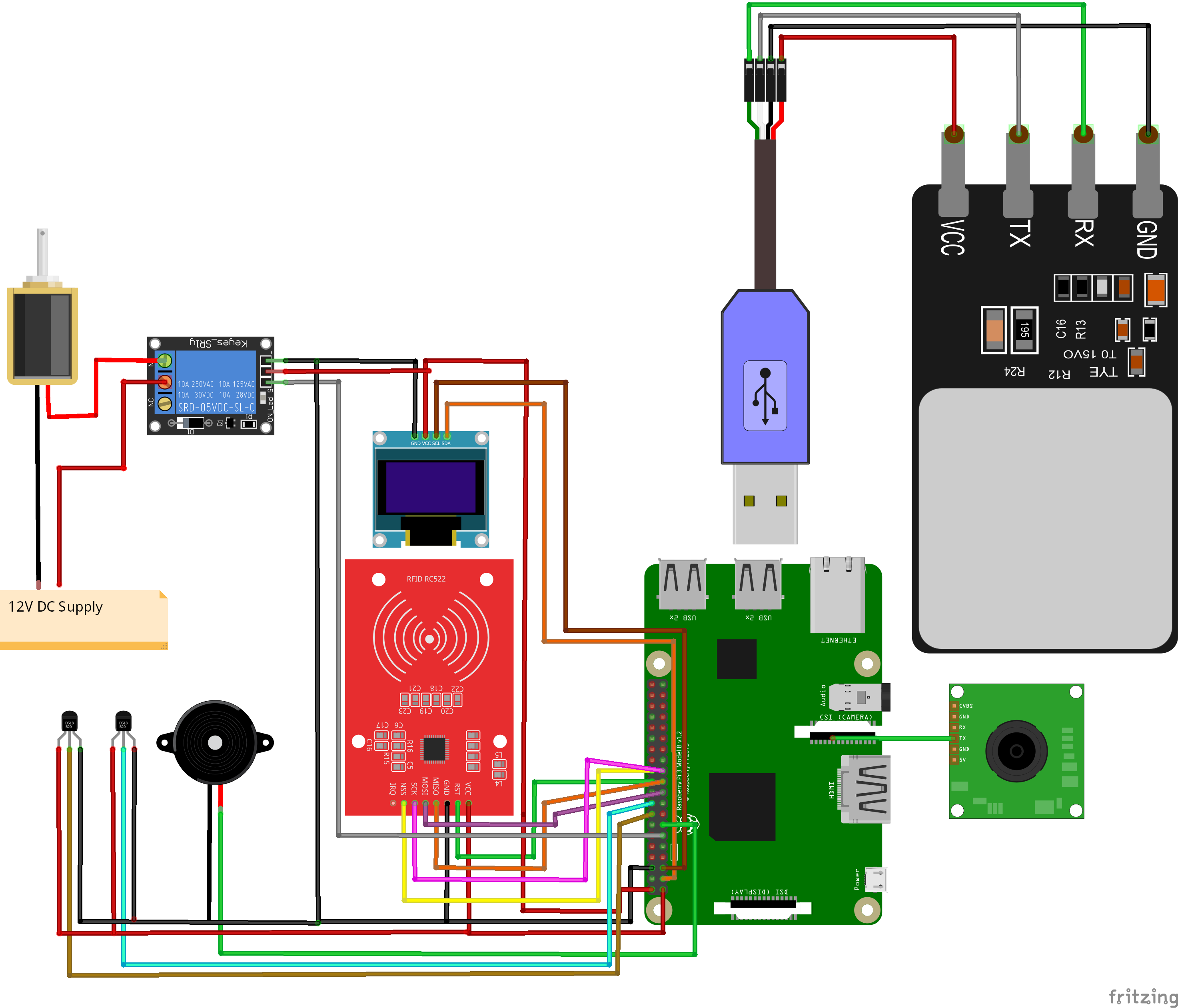
First contact the RFID card/tag to the RFID reader. Then place the finger on the fingerprint sensor and look at the camera to capture a photo of the user. Then the access will be granted if all there steps are correctly passed by that person. LCD display will display the information whether access has been given or not. All the accesses will be recorded on the website.
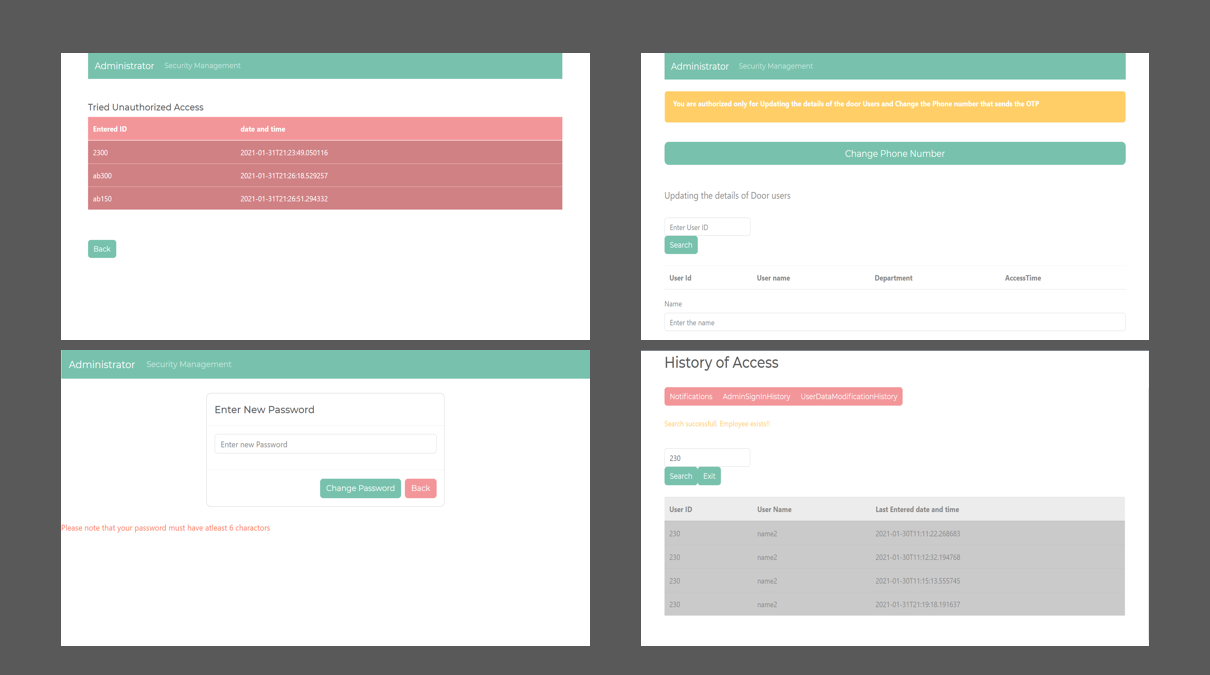
Identify Unauthorized Aceess
If any unauthorized access is detected i.e. using an unregistered card/tag or trying to access more than one person into the room using one card/tag, access will not be granted and the buzzer will make a loud sound. LCD display will display the information whether access has been given or not. These accesses will be recorded on the website.